
Coronavirus Breathes New Life Into Zeus Banking Trojan
By now, it’s clear that cybercriminals are ratcheting-up virus-related scams at a historic rate. Aside from the overabundance of coronavirus-related scam attacks, hackers are dusting off older malware, retooling it, and then deploying it with a vengeance. Such is the case with Zeus Sphinx, a banking Trojan from 2015 that faded away until very recently. A spawn of the infamous Zeus banking Trojan first discovered in 2007, Zeus Sphinx is bigger, better, and badder than ever.
Resurrected exclusively, it appears, to help exploit coronavirus fears, Zeus Sphinx hides its malware in phishing emails. And as a member of the Trojan banking family, Zeus Sphinx does what it does best––steal banking credentials. IBM X-Force spotted the banking Trojan in March of this year using coronavirus U.S. government economic impact relief payments as a bait. A malicious file named “COVID-19 relief” is attached to the email…and that’s where Zeus Sphinx is hiding. The emails claim it’s a form for those who can’t work during the pandemic to get “financial relief” from the government.
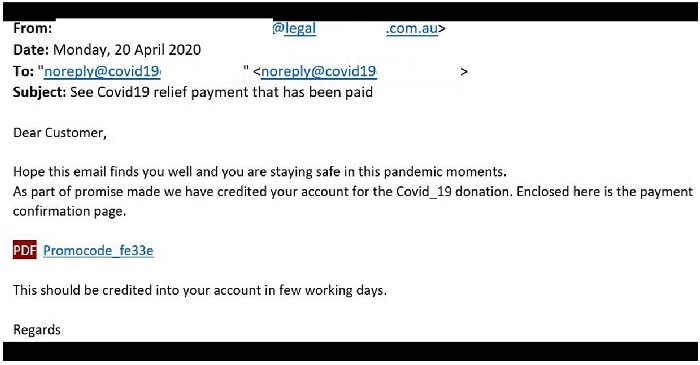
True to its Trojan roots, Zeus Sphinx harvests credentials from online banking sites. The attached “COVID-19 relief” form, usually in a .DOC or .DOCX format, modifies the page a user expects to see so it looks legitimate. Whatever personal data and account credentials are entered on the modified page is sent directly to waiting cybercriminals.
Once installed on a device, Zeus Sphinx spreads by writing itself onto files and folders, also creating registry keys. The registry keys get deposited into a system, making a device vulnerable to infection and corruption by the Trojan. The malware also uses a self-signed security certificate to avoid detection by anti-virus measures.
Fighting Back Against the Trojan
Since email phishing gives Zeus Sphinx life, using good email cyber-hygiene is a smart way to fight back against the Trojan. Below are anti-phishing reminders for the next time you receive an email promising government financial assistance (or any other coronavirus themes) using the pandemic as lures.
- Think before you click. Delete emails from unknown sources and question those from senders you know, especially if there are attachments or links and if you are not expecting them. Hackers use stolen contact lists to go phishing, so pick up a phone to verify the sender is really who they claim to be before opening attachments. Remember, better safe than sorry goes a long way in keeping cyber-secure.
- Keep device software up to date. Everything from browser, system, and anti-virus software should always be the latest version and applied as soon as its available. Make sure security patches are also kept updated ASAP as they often contain fixes for security bugs that hackers exploit. Consider setting your device to “automatic updates” to make sure you have the latest software versions installed.
- Make sure a website is secure. In particular, when the information you’re being asked to provide centers around finances or your identity, the website needs vetting before you act. Make sure the web address starts with “https://” and has a closed lock icon to the left side. When in doubt, type the organization’s true website name in yourself. Also, carefully check the spelling to make sure the website isn’t faked to phish your credentials.
From Stickley on Security

